ANTI THEFT SYSTEMS:
Anti-Theft Systems are devices which prevent unauthorized access to Cars or other mobile systems. The evolution of Anti-theft systems has ranged from simple key to RFID Tags, Bio metric Identification, and Palm Vein Recognition, etc.
The anti-theft systems are combination of smart sensors coupled with intelligent algorithms which can wisely distinguish between actual theft and fake ones. Upon detection of theft they immediately raise an alarm or notify the user with necessary details like geographical locations, time stamp , state of the device while theft occurred i.e.: If the anti-theft system is considered in automobiles , crucial data like whether the engine was turned on , doors were unlocked ,etc. are transmitted to the owner.
As the value of the goods such as Cars, Cell Phones, Laptops, etc. are increasing day by day. So is the risk of insecurity associated with them. In this article we shall look into functioning of Anti-Theft Systems and various components of the system, with few real time examples.
Block Diagram for Anti-Theft System:
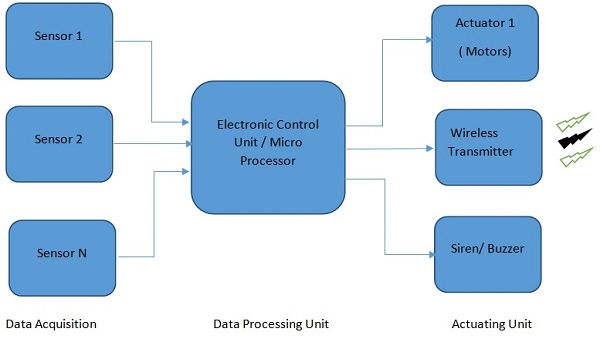
Fig. 1: Block Diagram Showing Anti-Theft System
Consider any general anti-theft system, it consists of above mentioned blocks at the minimum level.
Data Acquisition :
Here different environmental conditions surrounding the device to be protected is measured. Various data like identification, motion sensed, pressure, temperature are captured through smart sensors and are buffered into processing unit. The identification part plays a major role in data acquisition.
As the system permits full access to the device with proper authenticated users. Various types of authentication are possible. Finger Print identification which involves scanning of palm pattern and storing in form of binary image to latest one of palm recognition which is the most advanced secure technique though not in wide application yet, involves identification of each individual based on vein patterns in human hand.
With respect to anti-theft systems in automobiles, vehicle key plays an important role. Key along with the finger print /biometric identification provides a more robust secure channel which is intricate to hack.
Data Processing Unit :
Once the sensor data is received it is the task of the controller or the processor to validate the data and decide whether the theft is genuine and to raise an alert or not. The controller consists of signal processing unit which is required to filter out incoming noise from sensors and other ambient resources. Processors like ARM7 or dedicated ECUs in case of vehicles can be used.
When automobiles are fitted with keyless entry feature, the controller has a job to perform secure hash key computation which finds application in vehicle immobilizer which will be explained in later sections of the article. Apart from these there might exist an auxiliary processor which has the responsibility to communicate the user /owner wirelessly .Here the data is transmitted using Radio Waves usually as they are longer in range compared to other conventional sources such as Bluetooth ,ZigBee.
Actuating Unit :
Once the embedded intelligence confirm the theft, it is now time to alert the owner or surrounding public .As a part of this step, based on the situation an alarm can be triggered off along with vibration/electric shock .In case of vehicles if the thief tries to drive away the vehicle, doors and power windows can be locked. A more sophisticated system would send the location details to nearest police station through an SMS and also notify the owner through form of a mobile application, etc.
In further sections anti-theft systems with respect to vehicle is considered and elaborated in detail:
One such widely known system is Vehicle Immobilizer.
What is Vehicle Immobilizer?
An immobilizer or immobilizer is an electronic security device fitted to an automobile that prevents the engine from running unless the correct key (or other token) is present. This enhances the security of the car and prevents the vehicle from being hotwired.
Functioning of Vehicle Immobilizer:
The vehicle immobilizer makes use of electro magnetism to compute the key and authenticate itself as right user to Engine Management Module (ECM) .When a key is inserted into the vehicle. On the outer look it appears that vehicle just gets unlocked, a more scrutinized observation will help one understand the mechanism of working of Immobilizer.
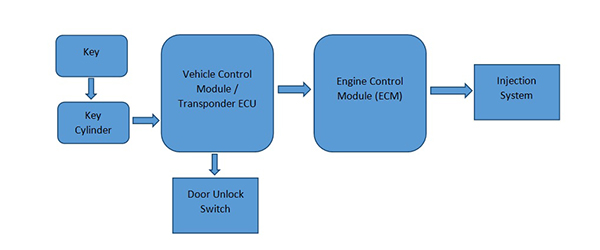
Fig. 2: Block Diagram Summarizing Functioning of Vehicle Immobilizer
· The operation of Immobilizer starts with insertion of a key into key cylinder.
· Once the key is inserted a microcircuit gets activated by a small electromagnetic field and induces a current to flow.
· A microchip that contains the unique key ID-number. Due to an encrypted request signal from the immobilizer control module the chip calculates a matching code for the ID-number before it is transferred.
· To prevent an unauthorized scanning of the ID-number the code changes with each transfer and uses several million different coding possibilities. – A coil, which transfers and receives all data signals to and from the immobilizer control module via the coil antenna / transceiver.
· Upon the flow of right amount of current the transponder ECU performs a computation which is different for different manufacturers, in computation it takes into account the time, current flowed by insertion and in few systems even biometric identification.
· Based on various inputs the transponder sends out a unique binary code to ECM module.
· If the code sent by transponder matches with one stored in ECM, the vehicle gets unlocked and ECM later sends request for unlocking vehicle doors, triggering injection system etc.
· Not only does the ECM unlock but in case of invalid key also prohibits engine getting started and prevents further ignition.
· Few vehicles even record the number of incorrect attempts and might lock the vehicle for ore determined interval of time.
One more such system is Remote less key Entry (RKE):
Theft of the vehicles is made more challenging by bringing in more complex techniques and algorithms. In RKE systems the functionality is embedded into vehicle control module. It employs challenge response protocol to perform the authentication between the key and car.
In this technique the car periodically keeps querying for the presence of the key using short beacons. Below is Passive Key Less Entry System (PKES).
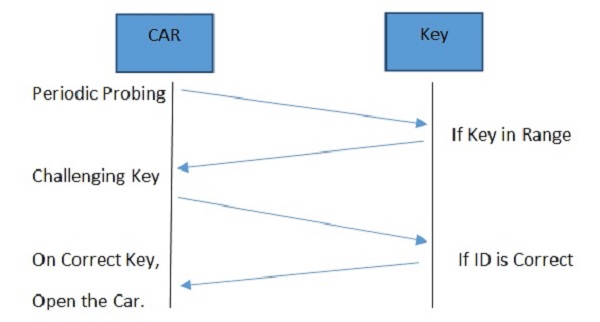
Fig. 3: Remoteless Key Entry System
Ø In challenge response protocol, the car monitors constantly for presence of the key by sending short bursts of signal (~ 120 – 135 kHz) to see if the key is in nearby region of car (typically ~100m).
Ø Once the key fob is in defined region of car, the car wakes up and demodulates the signals and interprets them.
Ø Then a response on that challenge is computed and replied on ultra-high frequency channel (315 -433 MHz)
Ø If the response is valid, the car unlocks the door. To start the engine the key must be inside the vehicle.
Issue with Keyless Remote Entry System:
The protective feature of Keyless entry was questioned by a team of researchers from ETH Zurich when they used Relay mechanism to intercept the signals emitted by Key Fob and the car .In this way the emitted signals were captured by Relay pairs and the car was made to believe that the Key is in vicinity of the Car, without breaking any cryptography the captured signal was now used to enter the vehicle and take control of the engine.
Summary:
· Anti-theft systems actively or passively monitor safety of the car and perform suitable actions.
· With most of the conventional systems in automobile getting replaced by X by wire, anti-theft systems have connectivity to internet /satellite.
· Immobilizer and Keyless entry do have few drawbacks such as power backup, cost factor, relay attack etc.
Filed Under: Articles


Questions related to this article?
👉Ask and discuss on EDAboard.com and Electro-Tech-Online.com forums.
Tell Us What You Think!!
You must be logged in to post a comment.